The Ultimate Guide to AI Network Security
- Ciaran Roche
AI’s promise and the pressure it puts on enterprise networks
Artificial intelligence is reshaping how enterprises think about productivity, decision-making, and digital experiences. The potential is significant: AI can elevate how teams operate, streamline complex processes, and unlock new capabilities across the business. Yet that promise only materializes when the underlying digital foundation can support it. If the network and security infrastructure are not equipped to meet the demands AI introduces, the benefits become inconsistent, and the risks escalate quickly.
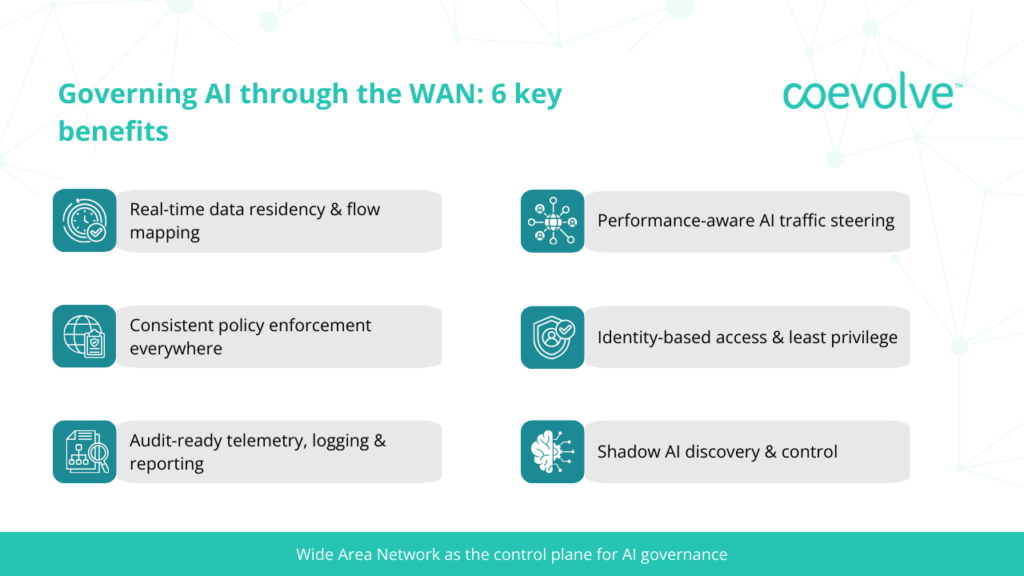
Insight: This is why the enterprise network and security architecture must operate as the control plane for AI governance – the layer that consistently manages how data moves, how users interact with AI tools, and how policies are enforced end‑to‑end.
In an era where agility, resilience, and innovation define competitive advantage, the enterprise network determines how effectively your business operates, scales, and transforms. Advanced capabilities like AI, edge computing, and cloud services can only deliver their full potential when built on a robust, adaptable foundation. Without rethinking the architecture beneath these innovations, organizations risk creating fragile ecosystems that hinder growth and expose vulnerabilities. The future isn’t just about adopting new technologies, it’s about engineering the infrastructure that makes them thrive.

James Halberstadt
Managing Director EMEA, Coevolve
How AI is fundamentally changing the enterprise WAN
AI is transforming the WAN in ways that go far beyond increased bandwidth consumption. Modern AI workloads introduce entirely new traffic behaviors that the traditional enterprise network was never engineered to handle. Instead of predictable, transactional flows between branch sites and data centers, AI generates dynamic, high-intensity interactions between users, cloud-hosted models, data lakes, SaaS providers, and third-party inference APIs. These interactions often involve large, sensitive datasets moving across multiple jurisdictions, elevating the importance of understanding where data travels, how it is protected, and what governance controls exist along the path.
As AI tools become embedded in everyday workflows, these new traffic patterns place new demands on enterprise networks, including low jitter, deterministic routing, region-aware egress, and visibility across historically opaque paths. Without these capabilities, even well-designed AI applications struggle to deliver consistent performance, especially when inference calls traverse continents or when model endpoints change dynamically based on provider load.
Additionally, AI tools carry some of the most sensitive data in the organization. Yet much of this traffic still moves across networks built for a perimeter-based world, where security is inconsistent, and visibility is limited. This gap creates real exposure. To keep pace, the security posture must evolve: inline inspection, identity-based access, and data-aware controls are no longer “nice to haves.” They are essential safeguards to prevent compliance failures and unintended data loss as AI adoption accelerates.
Insight: While AI is changing the enterprise WAN, the WAN is the only universal enforcement point – it’s where all AI usage becomes visible, classifiable, and governable, regardless of which tool, user, or endpoints initiates it.
The challenges of AI on enterprise networks
As the usage of AI inevitably grows, IT leaders are faced with 4 challenges that must be addressed early to keep deployments safe, auditable, and scalable.
Shadow AI
Stemming from the use of employees using chatbots, plug-ins, and AI features inside SaaS tools before governance catches up, likely resulting in sensitive inputs and outputs moving across the internet without being noticed. Because this looks like ordinary encrypted web use, traditional perimeter controls struggle to see or manage it, creating blind spots around who is using which AI service, what data is being shared, and where that data ultimately resides.
Insight: The network is the foundation for all applications in use, and is the logical point to monitor shadow AI use in real time. Addressing shadow AI starts with gaining visibility, understanding which AI applications are in use, by whom, and for what purpose. This visibility enables organisations to classify applications as approved, conditional, or prohibited, and to enforce policies consistently directly within the traffic flows on the network, rather than retroactively.
Data security and leakage
AI prompts, file uploads, and generated outputs frequently carry confidential or regulated information from customer records and IP to credentials and financials. When these interactions flow to public models or third-party services outside approved regions, organizations face both regulatory exposure and tangible operational risk.
Insight: A secure network will prevent sensitive data from leaving the enterprise through redacting or blocking, and use region-aware routing to ensure data residency requirements are met through controlled egress paths rather than post-hoc auditing. A holistic view of anomalies and mitigations allows the enterprise to align its response to regional regulations and best practices.
Governance and compliance
Policies may exist on paper, but are still enforced inconsistently across users, locations, and cloud applications. As AI adoption spreads, these inconsistencies compound: approvals are handled inconsistently, exceptions solidify into long-term risks, and audit trails fail to provide full accountability.
Insight: Anchor governance to identity (users, devices, and even automated agents) and to a clear set of data rules based on the user’s identity. Consistent policies can be enforced anywhere a user connects to the network, a significant improvement over traditional appliance-based models. This improves compliance in the enterprise, reducing the number of exceptions that need to be addressed.
AI attacks and vulnerabilities
AI dramatically widens the attack surface, making it easier for attackers to exploit vulnerabilities that look legitimate at first glance. Model manipulation, API abuse, and agent chaining can quickly lead to privilege escalation or rapid data loss.
Insight: Apply least‑privilege to apps and agents, rotate API keys, and shut down suspicious sessions in real time. Keep dev, test, and production environments isolated and tied only to approved model providers to contain any impact. Agent identity is as critical in this environment as user identity, and should be enforced consistently across the enterprise.
Is your network ready to govern AI?
As AI adoption accelerates across the organisation, the demands on your enterprise network and security architecture will intensify. Before scaling any AI initiative, it’s important to understand whether your current network and security environment can support the traffic patterns, data flows, governance requirements, and enforcement expectations that AI introduces. A mature network and security posture effectively becomes the enterprise’s control plane for AI governance, providing the visibility, enforcement, and data-path authority required to keep AI usage safe, compliant, and predictable.
Taking time to assess your organization’s readiness ensures that AI adoption is built on a network and security architecture that is resilient, consistent, and fully aligned with your governance priorities. Without this foundation, AI introduces new pressures on connectivity, visibility, access control, and data protection, and any gaps in these foundations can quickly turn into operational, compliance, or security risks.
More Thought Leadership



