The Ultimate Guide to Zero-Trust and Network Security: Principles, Benefits, and Best Practices
- Ciaran Roche
In today’s rapidly evolving digital landscape, traditional perimeter-based security approaches no longer suffice. With the proliferation of cloud services, remote work, and sophisticated cyber threats, enterprises must adopt more robust security frameworks.
Zero-trust security has emerged as a cornerstone of modern cybersecurity strategy, offering a comprehensive approach to protecting digital assets regardless of location or access mechanism.
What is zero-trust? Understanding its role in securing cloud and hybrid work environment
Zero-trust represents a paradigm shift in cybersecurity strategy, eliminating implicit trust from an organization’s security architecture. Unlike traditional security models that operate on the principle of “trust but verify,” zero-trust adopts a more stringent “never trust, always verify” approach. This fundamental change has become crucial as organizations transition to cloud-first and hybrid work environments.
Recent industry analysis from Gartner indicates that over 60% of organizations will embrace zero-trust as a starting place for security by 2025. However, more than half will fail to realize the benefits — initiating zero-trust requires more than technology.
This significant adoption rate reflects the growing recognition that traditional security perimeters have dissolved in the modern digital ecosystem, particularly as remote work and cloud computing become standard operational models for businesses.
The foundation of zero-trust security rests on continuous verification mechanisms that authenticate every user, device, and application attempting to access network resources.
This verification process occurs in real-time, ensuring that security policies are enforced consistently across all network interactions. Modern implementations leverage advanced authentication protocols and behavioral analytics to maintain security integrity while identifying anomalies and optimizing user experience.
Zero-trust fundamentals: The key principles driving modern network security
The zero-trust security model builds upon several foundational principles that collectively create a robust security framework. Understanding these principles is crucial for organizations considering centralised vs decentralised security approaches.
Identity-Centric Security
Identity serves as the new security perimeter in a zero-trust model. Every access request must undergo rigorous authentication and authorization processes, regardless of its origin. By implementing robust identity verification systems, organizations can significantly reduce unauthorized access attempts while maintaining operational efficiency.
Why zero-trust matters: The business benefits of enhanced network security
Organizations implementing zero-trust architecture experience substantial benefits that extend beyond improved security. The integration of AI and zero-trust helps address modern network security challenges while supporting maximizing the effectiveness of digital transformation initiatives.
The National Security Agency (NSA) emphasizes that zero-trust principles, including data encryption and rights management, can minimize downtime and operational impact by enabling fast recovery in the event of data loss or breaches.
Additionally, Microsoft’s security insights suggest that implementing a zero-trust framework helps organizations meet compliance and data security requirements, prevent and secure sensitive business data, and reduce business damage from breaches.
In 2026, the National Security Agency (NSA) released updated Zero Trust Implementation Guidelines, outlining a phased, structured approach to strengthening enterprise security. The guidance reinforces zero trust as a practical framework for improving visibility, limiting breach impact and enhancing organizational resilience.
Additionally, Microsoft’s Zero Trust guidance emphasises that implementing strong data protection, governance and least-privilege access controls helps organizations safeguard sensitive information, meet compliance obligations and reduce the operational impact of breaches.
In summary, while zero-trust architectures are widely recognized for improving security metrics and operational efficiency, specific quantitative improvements can vary based on individual organizational contexts and the comprehensiveness of the implementation.
Zero-trust and SASE: How they work together to simplify security infrastructure
The convergence of zero-trust and Secure Access Service Edge (SASE) creates a powerful security framework particularly relevant for SASE in hybrid work environments. Through strategic SASE integration, organizations can achieve comprehensive security coverage while maintaining operational agility.
As organizations progress with their SASE adoption, the synergy between zero-trust and SASE becomes increasingly important. This integration enables unified security policy management, reduced network complexity, and enhanced visibility across all access points, while improving user experience through simplified access protocols.
Overcoming challenges in zero-trust implementation
The journey to zero-trust implementation requires careful consideration of various challenges and strategic planning. A successful network and security strategy must address these challenges while effectively integrating multi-vendor SASE solutions.
Organizations must navigate legacy system integration complexities, resource constraints, and potential user resistance. Success requires a balanced approach that addresses technical requirements while ensuring user adoption and maintaining operational efficiency.
Future of zero-trust: Emerging trends in network security and beyond
The evolution of zero-trust security continues to accelerate, driven by emerging technologies and evolving threat landscapes. Recent trends in SD-WAN, SASE, and multi-cloud indicate significant developments in AI-driven security automation and enhanced IoT device security protocols.
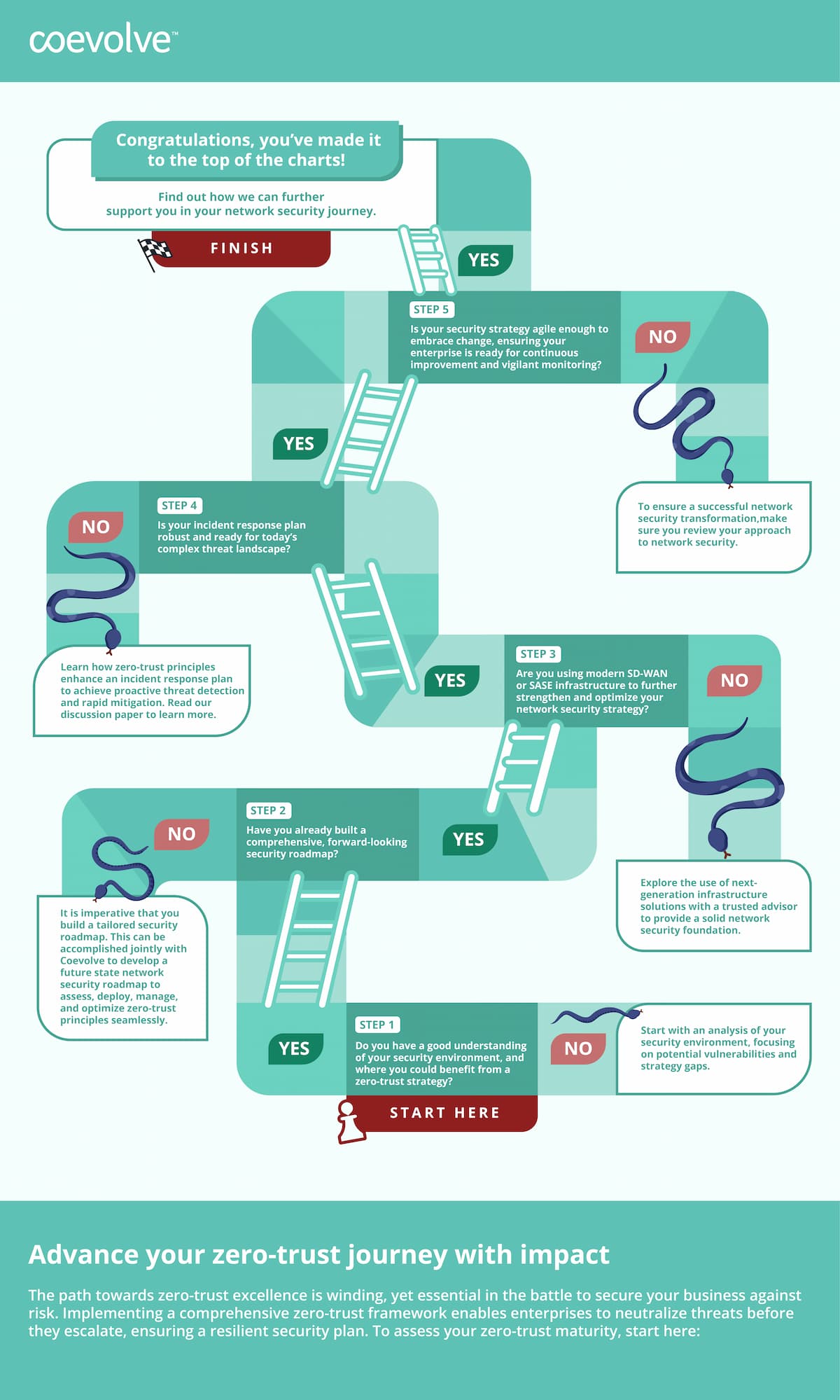
Implementing zero-trust in your organization
Successful zero-trust implementation requires a methodical approach focused on picking the best-fit solution for your organization’s specific needs.
Assessment and planning
The initial phase involves comprehensive security posture evaluation, detailed asset inventory, and thorough risk assessment. Organizations must analyze their current digital infrastructure, identify critical assets, and understand compliance requirements before proceeding with implementation.
Implementation strategy
Conclusion: The importance of zero-trust
As cyber threats continue to evolve and network environments become more complex, zero-trust security has transitioned from a theoretical concept to a business imperative. Organizations must adapt their security strategies to meet these challenges head-on.
Ready to enhance your organization’s security posture? Learn more about our Telco-Independent SASE solution and how it can help implement zero-trust security in your environment.
Table of contents
More Thought Leadership